Forensic investigation has confirmed the usage of Paragon’s Graphite adware platform in zero-click assaults that focused Apple iOS gadgets of a minimum of two journalists in Europe.
Researchers at Citizen Lab say that the victims have been a outstanding European journalists who requested anonimity and Ciro Pellegrino, a journalist at Italian publication Fanpage.it.
“Our evaluation finds forensic proof confirming with excessive confidence that each a outstanding European journalist (who requests anonymity), and Italian journalist Ciro Pellegrino, have been focused with Paragon’s Graphite mercenary adware,” studies Citizen Lab.
The assaults occurred in early 2025, and Apple despatched a notification to the 2 victims on April 29 informing that that they had been focused by “superior adware.”
The menace actor used Paragon’s Graphite adware platform to focus on the victims’ iPhone gadgets working iOS 18.2.1 and exploit CVE-2025-43200, which was a zero-day vulnerability on the time.
Apple describes the flaw as “a logic subject that existed when processing a maliciously crafted picture or video shared by way of an iCloud Hyperlink.”
The seller addressed the vulnerability within the subsequent iOS launch, 18.3.1, on February 10, by including improved checks. Nonetheless, the CVE identifier was added earlier in the present day to the safety bulletin .
BleepingComputer has reached out to Apple to make clear the date of fixing the vulnerability however haven’t acquired a response at publishing time.
In response to Citizen Lab’s evaluation, Graphite’s supply vector was iMessage. The attacker used an account, generically labeled ‘ATTACKER1’ within the analysis, to ship specifically crafted messages that exploited CVE-2025-43200 for distant code execution.
This achieved the supply of the adware with none interplay from the goal, in what known as a zero-click assault, and with out producing any seen indicators to alert the sufferer.
As soon as lively, the adware contacts a command-and-control (C2) server to obtain additional directions. Within the case confirmed by Citizen Lab, the contaminated cellphone linked to https://46.183.184[.]91, a VPS linked to Paragon’s infrastructure.
This IP tackle was hosted on EDIS World and was lively a minimum of till April 12.
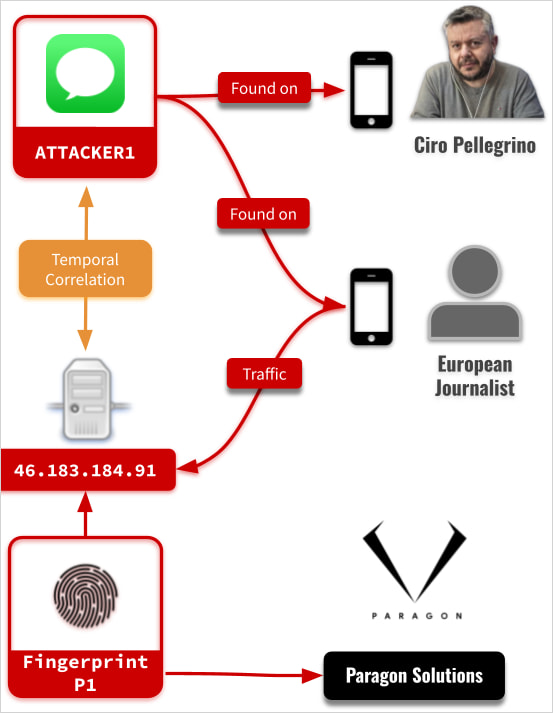
Supply: CitizenLabs
Though little hint was left on the gadgets, Citizen Lab was capable of recuperate some logs that contained sufficient proof to attribute the assaults to Paragon’s Graphite adware with excessive confidence.
The identical adware household was “caught” earlier this 12 months in one other zero-click assault exploiting a zero-day vulnerability in WhatsApp that focused different Italian victims.
Italian authorities have confirmed earlier this month a number of assaults in opposition to people within the nation, together with journalist Francesco Cancellato and activists Luca Casarini and Dr. Giuseppe “Beppe” Caccia. Nonetheless, the events chargeable for these assaults aren’t publicly identified presently.
Patching used to imply complicated scripts, lengthy hours, and limitless fireplace drills. Not anymore.
On this new information, Tines breaks down how fashionable IT orgs are leveling up with automation. Patch sooner, cut back overhead, and give attention to strategic work — no complicated scripts required.


