New particulars have emerged a couple of phishing marketing campaign concentrating on Chrome browser extension builders that led to the compromise of at the very least thirty-five extensions to inject data-stealing code, together with these from cybersecurity agency Cyberhaven.
Though preliminary studies centered on Cyberhaven’s security-focused extension, subsequent investigations revealed that the identical code had been injected into at the very least 35 extensions collectively utilized by roughly 2,600,000 folks.
From studies on LinkedIn and Google Teams from focused builders, the most recent marketing campaign began round December fifth, 2024. Nonetheless, earlier command and management subdomains discovered by BleepingComputer existed way back to March 2024.
“I simply wished to alert folks to a extra refined phishing electronic mail than ordinary that we bought that said a Chrome Extension coverage violation of the shape: ‘Pointless particulars within the description’,” reads the submit to Google Group’s Chromium Extension’s group.
“The hyperlink on this electronic mail appears to be like just like the webstore however goes to a phishing web site that may attempt to take management of your chrome extension and sure replace it with malware.”
A misleading OAuth assault chain
The assault begins with a phishing electronic mail despatched to Chrome extension builders straight or by means of a assist electronic mail related to their area title.
From emails seen by BleepingComputer, the next domains have been used on this marketing campaign to ship the phishing emails:
supportchromestore.com
forextensions.com
chromeforextension.com
The phishing electronic mail, which is made to look as if it comes from Google, claims that the extension is in violation of Chrome Net Retailer insurance policies and is prone to being eliminated.
“We don’t permit extensions with deceptive, poorly formatted, non-descriptive, irrelevant, extreme, or inappropriate metadata, together with however not restricted to the extension description, developer title, title, icon, screenshots, and promotional pictures,” reads the phishing electronic mail.
Particularly, the extension’s developer is led to consider their software program’s description comprises deceptive info and should conform to the Chrome Net Retailer insurance policies.
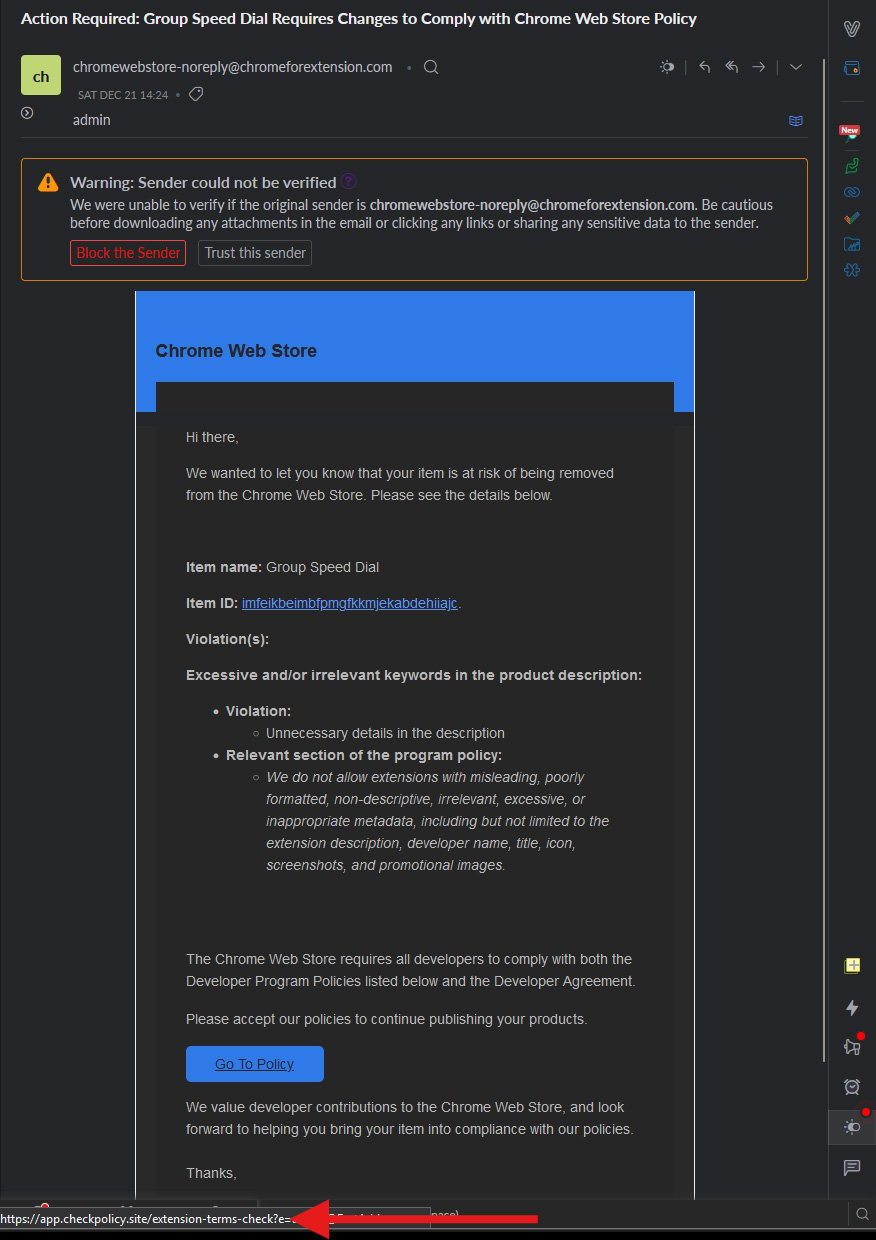
Supply: Google Teams
If the developer clicks on the embedded ‘Go To Coverage’ button in an effort to grasp what guidelines they’ve violated, they’re taken to a professional login web page on Google’s area for a malicious OAuth utility.
The web page is a part of Google’s commonplace authorization circulation, designed for securely granting permissions to third-party apps to entry particular Google account assets.
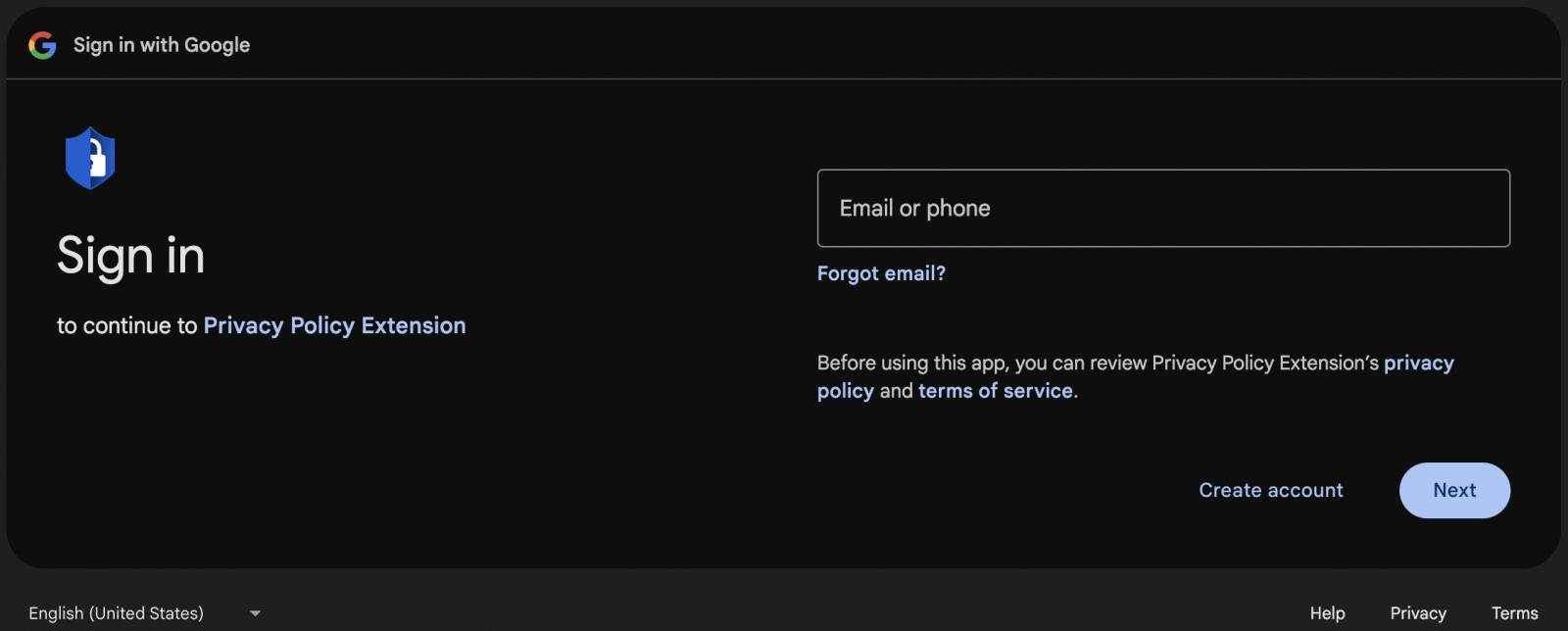
Supply: Cyberhaven
On that platform, the attacker hosted a malicious OAuth utility named “Privateness Coverage Extension” that requested the sufferer to grant permission to handle Chrome Net Retailer extensions by means of their account.
“Whenever you permit this entry, Privateness Coverage Extension will have the ability to: See, edit, replace, or publish your Chrome Net Retailer extensions, themes, apps, and licenses you’ve gotten entry to,” reads the OAuth authorization web page.
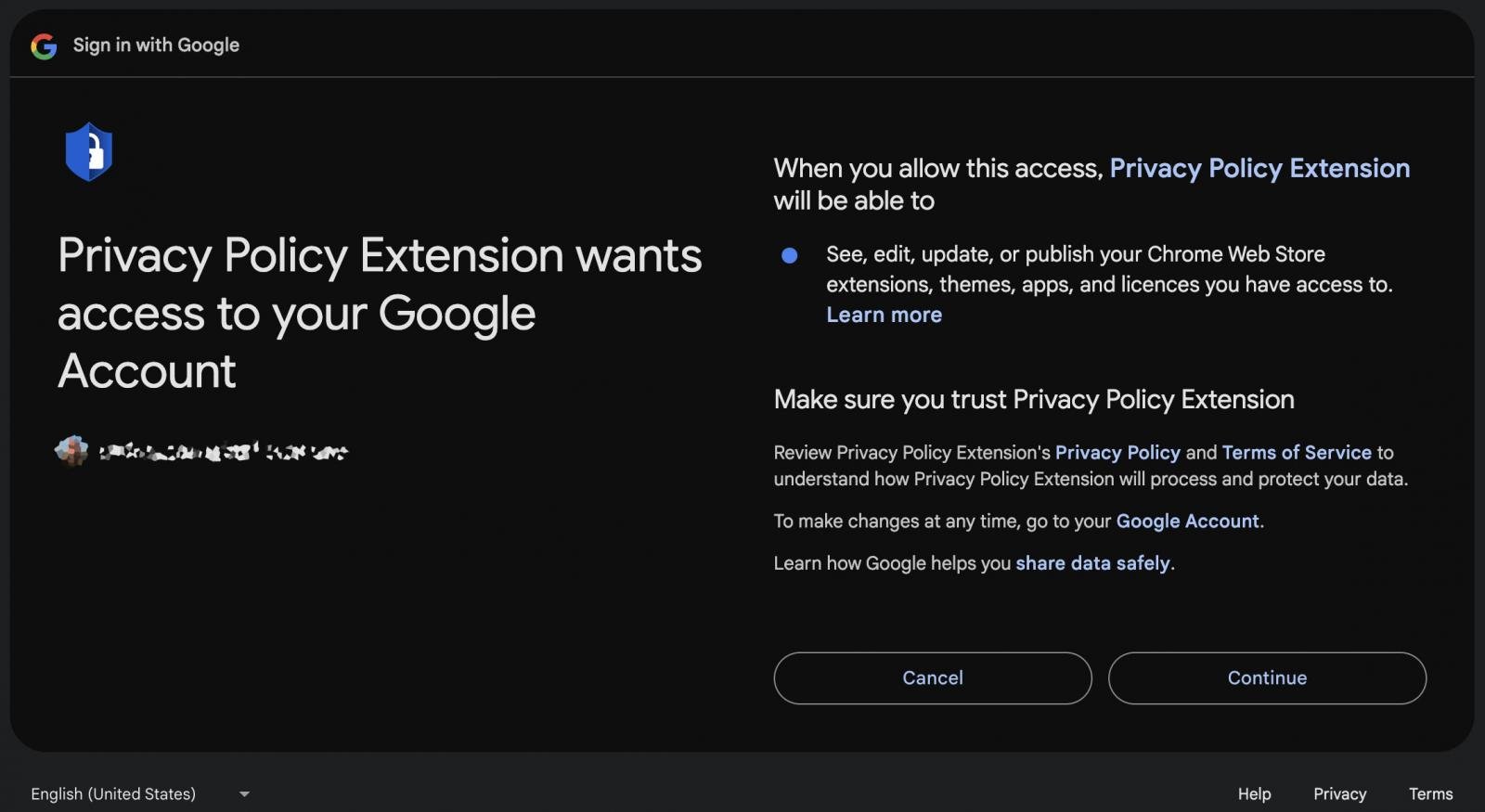
Supply: Cyberhaven
Multi-factor authentication did not assist defend the account as direct approvals in OAuth authorization flows aren’t required, and the method assumes the consumer totally understands the scope of permissions they’re granting.
“The worker adopted the usual circulation and inadvertently licensed this malicious third-party utility,” explains Cyberhaven in a autopsy writeup.
“The worker had Google Superior Safety enabled and had MFA protecting his account. The worker didn’t obtain an MFA immediate. The worker’s Google credentials weren’t compromised.”
As soon as the menace actors gained entry to the extension developer’s account, they modified the extension to incorporate two malicious recordsdata, specifically ’employee.js’ and ‘content material.js,’ which contained code to steal knowledge from Fb accounts.
The hijacked extension was then printed as a “new” model on the Chrome Net Retailer.
Whereas Extension Whole is monitoring thirty-five extensions impacted by this phishing marketing campaign, IOCs from the assault point out {that a} far higher quantity have been focused.
Based on VirusTotal, the menace actors pre-registered domains for focused extensions, even when they didn’t fall for the assault.
Whereas most domains have been created in November and December, BleepingComputer discovered that the menace actors have been testing this assault in March 2024.
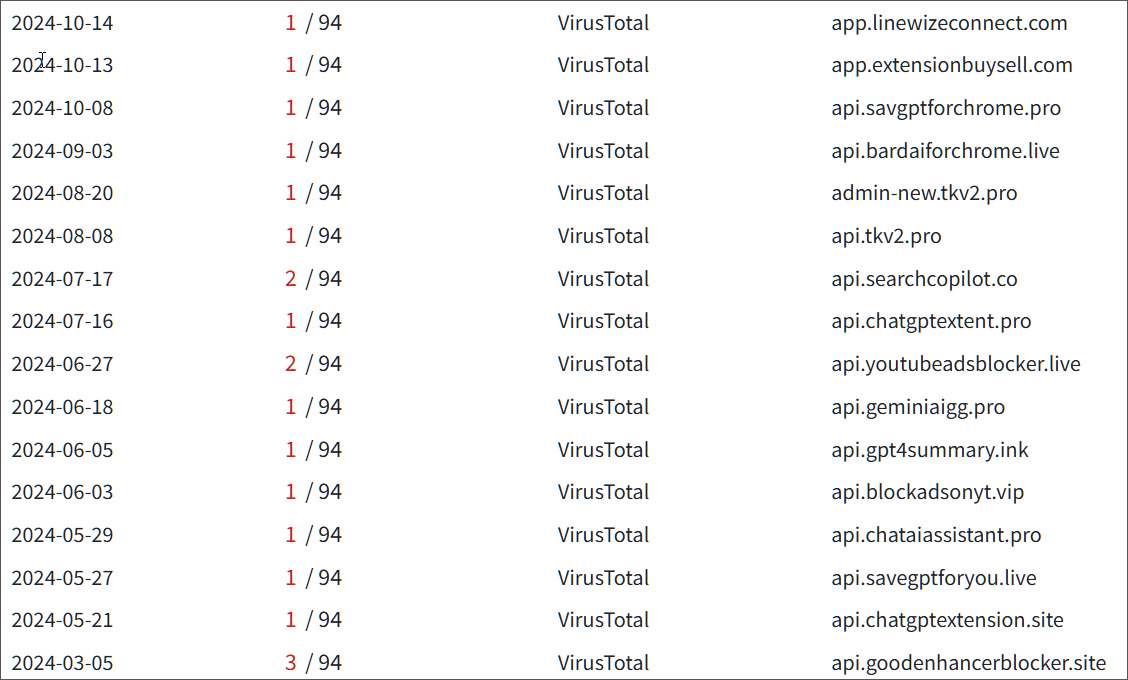
Supply: BleepingComputer
Concentrating on Fb enterprise accounts
Evaluation of compromised machines confirmed that the attackers have been after the Fb accounts of customers of the poisoned extensions.
Particularly, the data-stealing code tried to seize the consumer’s Fb ID, entry token, account data, advert account info, and enterprise accounts.

Supply: Cyberhaven
Moreover, the malicious code added a mouse click on occasion listener particularly for the sufferer’s interactions on Fb.com, searching for QR code pictures associated to the platform’s two-factor authentication or CAPTCHA mechanisms.
This aimed to bypass 2FA protections on the Fb account and permit the menace actors to hijack it.
The stolen info can be packaged along with Fb cookies, the consumer agent string, Fb ID, and the mouse click on occasions and exfiltrated to the attacker’s command and management (C2) server.
Menace actors have been concentrating on Fb enterprise accounts through numerous assault pathways to make direct funds from the sufferer’s credit score to their account, run disinformation or phishing campaigns on the social media platform, or monetize their entry by promoting it to others.

